Passwordless Authentication Tools Like Okta That Help You Eliminate Password Risks
Passwords have long been the gatekeepers of our digital lives—but they’re also one of the weakest links in cybersecurity. From phishing attacks to credential stuffing and data breaches, traditional password-based systems create more risk than protection. As cyber threats grow more sophisticated, businesses are turning to passwordless authentication tools like Okta to enhance security, simplify user access, and reduce IT burdens.
TLDR: Passwordless authentication eliminates the risks tied to weak or stolen passwords by using secure methods such as biometrics, hardware tokens, and one-time passcodes. Tools like Okta, Microsoft Entra ID, Duo, and Auth0 help businesses strengthen security while improving user experience. These solutions reduce phishing risks, lower IT support costs, and streamline login processes. Moving to passwordless is fast becoming a cybersecurity best practice for modern organizations.
The shift away from passwords isn’t just a trend—it’s a strategic necessity. In this article, we’ll explore how passwordless authentication works, why it matters, and which leading tools can help your organization eliminate password-related risks.
Why Passwords Are a Security Liability
Passwords have been the standard authentication method for decades. However, they come with several well-documented weaknesses:
- Weak or reused passwords: Users frequently recycle passwords across multiple platforms.
- Phishing attacks: Attackers trick users into revealing login credentials.
- Credential stuffing: Stolen credentials are used to breach multiple accounts.
- High support costs: IT teams spend significant time handling password resets.
According to cybersecurity research, compromised credentials remain one of the most common causes of data breaches. Every password represents a potential attack surface. The more credentials you manage, the greater the risk exposure.
Passwordless authentication directly addresses these vulnerabilities by removing passwords entirely from the login process.

What Is Passwordless Authentication?
Passwordless authentication verifies a user’s identity without requiring them to enter a password. Instead, it uses alternative authentication factors such as:
- Biometrics: Fingerprint or facial recognition
- Hardware tokens: Security keys like YubiKey
- Magic links: One-click email login links
- Push notifications: Approvals sent to trusted devices
- One-time passcodes (OTP): Time-limited codes via app or SMS
- FIDO2 and WebAuthn standards: Cryptographic authentication protocols
These methods rely on something the user has or is, rather than something they know. Because there’s no password to steal or reuse, attackers have far fewer opportunities to exploit accounts.
How Okta Leads the Passwordless Movement
Okta is one of the most recognized identity and access management (IAM) platforms offering passwordless solutions. Designed for enterprises, it integrates seamlessly across cloud and on-premises environments.
Key passwordless features in Okta include:
- Okta FastPass: Phishing-resistant authentication without passwords
- Biometric login: Support for device-level biometrics
- Adaptive multi-factor authentication (MFA): Context-aware security policies
- Single sign-on (SSO): Seamless access across applications
- FIDO2 WebAuthn support: Security key compatibility
Okta’s strength lies in its flexibility. Organizations can gradually transition from passwords to passwordless models while maintaining tight security controls.
Other Leading Passwordless Authentication Tools
While Okta is a heavyweight in identity management, several other platforms provide robust passwordless capabilities. Here’s a closer look at top contenders:
1. Microsoft Entra ID (formerly Azure AD)
- Passwordless phone sign-in
- Windows Hello biometric authentication
- FIDO2 security key integration
- Strong enterprise ecosystem integration
2. Duo Security (Cisco Duo)
- Push-based authentication
- Biometric verification
- Device trust policies
- Zero Trust framework support
3. Auth0 (by Okta)
- Magic link login
- Passwordless SMS and email authentication
- Developer-friendly APIs
- Customizable authentication flows
4. Ping Identity
- FIDO-enabled authentication
- Risk-based adaptive authentication
- Enterprise-grade identity orchestration
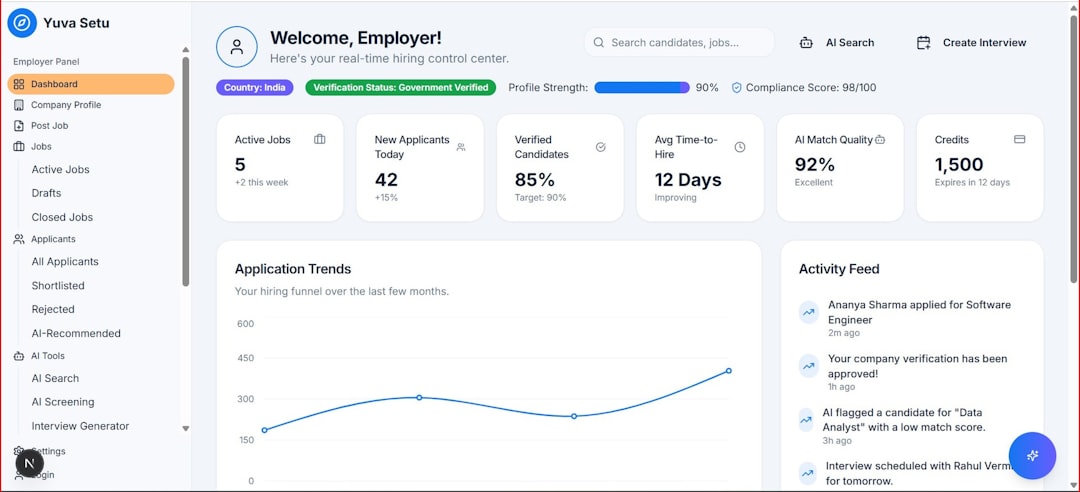
Passwordless Authentication Tools Comparison Chart
| Tool | Best For | Biometrics Support | FIDO2 Support | SSO Included | Adaptive Policies |
|---|---|---|---|---|---|
| Okta | Enterprise environments | Yes | Yes | Yes | Yes |
| Microsoft Entra ID | Microsoft ecosystem users | Yes | Yes | Yes | Yes |
| Duo Security | Zero Trust security models | Yes | Yes | Limited | Yes |
| Auth0 | Developers and SaaS apps | Limited | Yes | Yes | Yes |
| Ping Identity | Large enterprises | Yes | Yes | Yes | Yes |
Key Benefits of Going Passwordless
1. Enhanced Security
Passwordless systems eliminate common attack vectors such as password spraying and phishing. Since credentials aren’t stored centrally in the same way passwords are, large-scale breaches become significantly harder.
2. Better User Experience
Logging in with a fingerprint or approving a push notification is faster and more convenient than typing complex passwords. This seamless experience improves productivity and reduces login friction.
3. Lower IT Support Costs
Password resets consume considerable IT resources. Removing passwords drastically cuts helpdesk tickets and administrative overhead.
4. Compliance and Regulatory Support
Passwordless authentication aligns with modern compliance standards emphasizing multi-factor and phishing-resistant authentication methods.
5. Scalability for Hybrid Workforces
With remote work now commonplace, secure access across devices and locations is critical. Passwordless solutions provide scalable security for distributed teams.
How Passwordless Supports Zero Trust Security
Zero Trust architecture operates on the principle of “never trust, always verify.” Passwordless authentication complements this model by ensuring:
- Continuous verification of identity
- Device trust validation
- Context-aware authentication (location, behavior, risk level)
- Least-privilege access enforcement
By integrating passwordless technology into Zero Trust frameworks, organizations reduce lateral movement risks within networks.
Challenges to Consider Before Transitioning
While passwordless authentication offers clear benefits, implementation requires thoughtful planning:
- Legacy system compatibility: Older applications may require integration adjustments.
- User adoption: Training may be needed for smooth onboarding.
- Device dependency: Biometric methods rely on modern device support.
- Backup methods: Organizations should maintain secure fallback options.
A phased rollout strategy often works best. Many organizations initially deploy passwordless methods alongside traditional credentials, gradually phasing out passwords as confidence grows.
Best Practices for Implementing Passwordless Authentication
To maximize effectiveness and security, consider these proven strategies:
- Adopt FIDO2 standards: Choose phishing-resistant authentication mechanisms.
- Enable adaptive authentication: Adjust security requirements based on risk.
- Implement device management policies: Ensure endpoints are secure.
- Train employees: Educate users on authentication best practices.
- Monitor continuously: Use analytics to detect anomalies.
Combining passwordless authentication with strong governance policies creates a powerful defense against evolving cyber threats.
The Future Is Passwordless
Major technology companies are actively pushing for a password-free future. Industry-wide support for FIDO standards and biometric authentication shows a collective commitment to eliminating passwords altogether.
As digital ecosystems expand—with more apps, devices, and remote users—traditional passwords simply can’t keep up with the security demands of modern organizations. Passwordless authentication tools like Okta and its competitors are paving the way for safer, more efficient identity management.
For businesses serious about reducing breach risks while boosting user convenience, passwordless solutions aren’t just an upgrade—they’re an evolution in cybersecurity strategy.
In a world where stolen credentials fuel the majority of cyberattacks, removing passwords from the equation may be the smartest security decision you can make.

Comments are closed, but trackbacks and pingbacks are open.